Swifties, this one’s for you. It seems like Taylor Swift's Eras Tour has lasted eons. Yet somehow, there’s always something to talk about. Just thinking about how much she’s accomplished while on tour makes me want to buckle down, lock in, and channel my inner girlboss. But while I can’t even be bothered to cook dinner at home after a long day of work, Taylor is accomplishing milestones most musicians can only dream of. Let’s recap.
The Era’s Tour began in March 2023 with its North American leg. It’s set to go until December 2024, with dates in Europe, Australia, Asia, and South America— spanning 152 shows across five continents.
As the queen of multitasking, Swift hasn’t stopped at just selling out stadiums. Since the Eras tour began, she’s released multiple albums — both new and old — and shaken up the tour setlist with each new release. Her list of new releases started on the first day of tour with “All Of The Girls You Loved Before,” which was quickly followed up by “The Alcott,” a feature on The National’s album — reciprocity for their work on her pandemic era albums, Folklore and Evermore.
She also released Midnights: Late Night Edition (including the iconic collab with Ice Spice), as well as not one but two album re-releases — Speak Now Taylor's Version and 1989 Taylor's Version. As if that wasn’t enough, she announced her latest album, The Tortured Poet’s Department, in a GRAMMY’s acceptance speech. Talk about legendary. Since its release, she’s also been churning out deluxe versions and remixes to keep us on our toes. The Eras Tour was even made into a Blockbuster film that brought Beyonce to its premiere. Star power: confirmed.
But that’s just her work life. Her personal life is just as eventful. She ended her 7-year relationship with Joe Alwyn in April 2023. Then entered into a brief but controversial fling with 1975 frontman Matty Healy. Though it didn’t last long, the relationship was enough to inspire a whole album and catapult her into her current romance with Travis Kelce, aka Amerca’s first nepo boyfriend. Now they’re the American Royal couple — and she somehow had time to fly from tour to his Super Bowl performance.
We all have the same hours in the day as Taylor Swift, but how she uses them will always be a mystery to me. I work eight hours a day and can barely manage a social life. Meanwhile, Taylor literally has it all — though conservatives are turning on her for daring to be a woman in her 30s who’s not married with kids. If that’s not proof that women can’t do anything right, I don’t know what is.
Clearly, she’s working late because she’s a singer. No wonder Taylor Swift became a billionaire months into her tour in October 2023. Her net worth is currently around 1.3 billion dollars, making her the only female musician to become a billionaire from her music.
Other entertainment billionaires like Rihanna, Kylie Jenner, Kim Kardashian, Jay-Z, and Kanye West have joined the three-comma club thanks to ventures like clothing brands, beauty products, and other entrepreneurial pursuits. Rihanna has her FENTY Empire. Kim has her award-winning SKIMS. Ye had Yeezy. But Taylor has an unbeatable catalog of publishing.
But Taylor isn’t just different from other Billionaires because of how she earned her money. She’s the Taylor we know and love because of how she spends it. Her rollercoaster Eras Tour is how she’s made much of her fortune. And she’s using it to give back in monumental degrees. From individual donations to investing in local infrastructure, Taylor is literally changing lives on a macro and micro scale. And teaching us what to expect from all billionaires in the process.
The Era’s Tour Bonuses — Talk About Workplace Benefits
First to make headlines were the Eras Tour crew bonuses. While some of us get rewarded with a pizza party or a $10 gift card to Starbucks, Taylor casually dropped $55 million in bonuses for her tour crew. The massive sum was paid out to everyone who makes the Eras Tour go around, from truck drivers to dancers and sound technicians.
In fairness, these bonuses are definitely well-deserved. Taylor’s shows are over three hours long. Imagine dancing for that long — because Swift certainly isn’t the one with the impressive moves — for hundreds of tour dates. Or remembering countless combinations of light cues to go with a setlist that changes daily. Yeah, they’re clocking in. And if my boss had millions to blow, I’d be expecting a comfortable bonus too. But $55 Million? That’s a testament to Swift’s generosity. It's like she's Oprah, but instead of cars, she's giving out life-changing amounts of cash. "You get a bonus! You get a bonus! Everybody gets a bonus!"
It’s similar to how Zendaya gave film equity to every member of the crew that worked on her controversial black-and-white drama, Malcolm & Marie. Filmed in a few days with a bare-bones crew during the peak of the pandemic, the film was Zendaya’s passion project with Sam Levinson, in which she starred alongside John David Washington. Though the film got mixed reviews, it captured the audience’s attention all the same. After all, it was Zendaya — and we’ll watch her in anything. So since the film sold to Netflix for a hefty sum, all the crew members got payouts from the deal on top of their salaries to reward their hard work.
Bonuses and equity payouts are common in many industries, but not entertainment. Even though it’s one of the most lucrative and recognizable American industries, most entertainers don’t make enough to survive. The SAG and WGA strikes last year were proof that there needs to be systemic change in the industry. LA County has even identified show businesses as risk factors for being unhoused — after all, how many stories do we hear of actors who were living in their cars before their big break? And for many, their big break never comes. For even more, they get hired on amazing gigs with giant performers … then go right back to the grind afterward. While individual actions from our favorite stars won’t fix everything, Zendaya and Taylor are providing models for how Hollywood should treat the people who make this town go round.
And in this economy, even a little bit could go a long way. Inflation and the cost of living are not a joke. Especially when, like with many creative careers, you often have to invest in lessons or equipment for your craft. With all this considered, the impact of Swirt’s donations can’t be overstated. Imagine getting a lump sum of cash for dancing to your favorite Taylor Swift tracks? Talk about a dream job.
The Economic Impact of Swift - Swiftonomics, if you will
Like Barbie and Beyonce last year, Swift is still on a tear to boost the economy of the cities she’s in just by traveling there — ad inspiring others to make the trek, too.
The Barbie movie proved that by marketing to women (instead of just making Marvel flops like Madame Web that aren’t really targeted to women at all), the entertainment industry can make giant profits. Barbie fever went beyond the theater. Thanks to a plethora of product collabs, the phenomenon rippled through retail.
Similarly, Beyonce’s Renaissance Tour tour generated an estimated $4.5 billion for the American economy. According to NPR, that’s almost as much as the entire 2008 Olympics earned for Beijing. People were taking money out of their 401ks to pay for Beyonce tickets and the glittery, silver-hues outfits to rock at her shows. Cities even started calling her effect the “Beyonce Bump.”
Swift has the same effect. She’s not just proving her generosity on a micro-scale for the people close to her, she’s having actual, tangible effects on the economy. It's like she's leaving a trail of dollar bills in her wake, and cities are scrambling to catch them like it's a country-pop, capitalist version of musical chairs.
The US Travel Association called it the Taylor Swift Impact after she generated over $5 Billion in just the first 5 months of the Eras Tour. But how does this work? It’s not like Taylor is printing more money at those shows, but it almost is. Her tour dates are pretty much economic steroid shots for local businesses. Hotels are booked solid, restaurants are packed, and let's not even get started on the surge in friendship bracelet supplies.
“Swifties averaged $1,300 of spending in local economies on travel, hotel stays, food, as well as merchandise and costumes,” say the US Travel Association. “That amount of spending is on par with the Super Bowl, but this time it happened on 53 different nights in 20 different locations over the course of five months.” That’s not to say anothing of her effect on the actual Super Bowl and the entire NFL season thanks to her ball-throwing boyfriend.
It's like she's created her own micro-economy, and everyone's invited to the party. And unlike some economic theories that rely on wealth trickling down (spoiler alert: it doesn't), Taylor's wealth is more like a t-shirt cannon or the confetti at her shows — showering everyone around.
Donations that actually do good
Taylor isn’t just stepping into cities and calling it a night. She’s also not just throwing pennies at problems - she's making significant contributions that are changing lives. And more importantly, she's using her platform to encourage her fans to do the same.
She kicked off her tour with quiet donations to food banks in Glendale, Ariz., and Las Vegas ahead of the Eras Tour. Once the tour was in full swing, she continued this practice. In Seattle, she donated to Food Lifeline, a local hunger relief organization. In Santa Clara, she showed some love to Second Harvest of Silicon Valley. And let's not forget about her $100,000 donation to the Hawkins County School Nutrition Program in Tennessee.
She’s been making similar donations overseas. Taylor Swift donated enough money to cover the food bills for an entire year across 11 food banks and & community pantries in Liverpool. Swift also covered 10,800 meals for Cardiff Foodbank and many more banks across the UK and EU. Her impact is so profound that her numbers are doing more to combat issues like hunger than the government.
Can billionaires actually be good?
One thing about me, I’m always ready and willing — knife and fork in hand — to eat the rich. Because fundamentally, can any billionaire really be good? In our late-stage capitalist horror story, the answer is usually no. Look how many of them are supporting the Trump campaign just to get some tax breaks.
But here's the thing - Taylor Swift might just be the exception that proves the rule. She's not perfect, sure. She still flies private jets and probably has a carbon footprint bigger than Bigfoot. But unlike most of the others in her tax bracket, she's not flaunting her wealth like it's a personality trait.
Take a look around. We've got billionaires trying to colonize Mars instead of, I don't know, helping people on Earth. In this context, Taylor's approach is more like Mackenzie Scott’s — Bezos’s ex-wife. She's not trying to escape to another planet - she's trying to make this one better.
And look, I'm not saying we should stop critiquing billionaires or the system that creates them. But she's just setting the bar for what we should expect from all billionaires. She's showing us that our collective power as fans can translate into real-world change. That our love for catchy choruses and bridge drops can somehow, improbably, lead to food banks getting funded and crew members getting life-changing bonuses.
So sorry to my neighbors who hear me belting “Cruel Summer” and “right where you left me” at the top of my lungs (and range). Just know it’s for the greater good.
We Are Anonymous: A Brief History of the Internet's Most Elusive Hacktivist Collective
Ideas are indestructible, and Anonymous was always—first and foremost—an idea.
Once upon a time, the Internet was less a broken mirror of reality and more a diversion from it.
Maybe that's why prior to the era of identity monetization, blue check marks, and self-branding, anonymity was synonymous with power.
In the early 2000s, a group known as Anonymous sprung up across digital platforms, born out of a spirit of loose anarchism and disruption. "Anonymous" or "Anon" is an umbrella term, and like the Internet itself, the group was always slippery and amorphous.
Between 2003 and 2018, Anonymous's loosely interconnected network of digital hacktivists took on everything from Scientology to the Clintons to ISIS to Trump. At some point, they fractured, and it's unclear as to whether they still exist in any context, or if they ever really did. Was Anonymous an idea? A joke? A movement?
To try and answer these questions is a doomed enterprise from the start because the group is (or was) so decentralized, so scattered, and so complex that it resists exact interpretation.
But perhaps Anonymous can also teach us something about our modern political moment—after all, the group was entwined with many of the major political forces of the past decade, from Occupy Wall Street to the Arab Spring to QAnon. Maybe it can teach us something about the art of modern rebellion, especially in a rapidly digitizing and artificial age when information is poised to become the most valuable currency of all.
Welcome to the netherworld of Anonymous, where everyone can be no one together.
Born of Trolls, Hackers Turn to Scientology
The hacktivist network known as "Anonymous" arose around 2003. Springing up on 4chan, the group began as a collective of tricksters harnessing the Internet to pull pranks and seed an ethos of trolling and general disarray.
Anonymous eventually gained global reach thanks to its appealing ethos of decentralized leadership and general anarchical spirit. With memetic virality, it spread thanks to broad, decentralized messaging techniques and an emphasis on both humor and justice.
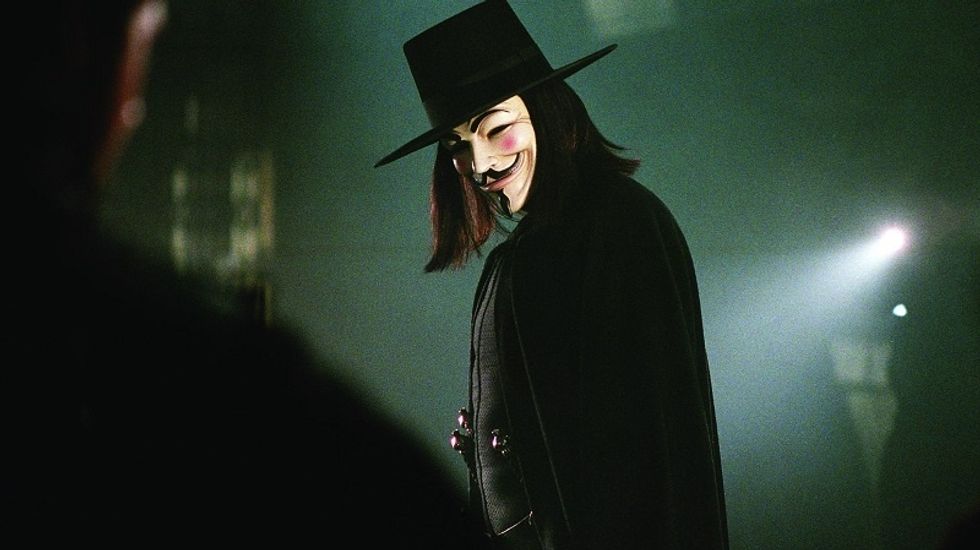
Today, two images are usually associated with Anonymous. There's the Guy Fawkes mask from the 2006 film V for Vendetta, which follows one activist's quest to end a totalitarian fascist rule in England; and there's the "man without the head" image that symbolizes the group's commitment to decentralized, anti-authoritarian rule.
 Literary Hub
Literary Hub
Early on, the group embarked on helter-skelter actions and pranks, with mixed results. The group targeted the white nationalist figure Hal Turner in 2006, eventually exposing him as an FBI informant, and Anonymous first began to dive into high-profile political activism through an effort called "Project Chanology," a coordinated protest against the Church of Scientology. After the Church removed a video of Tom Cruise because they believed it portrayed them negatively, Anonymous hackers started a campaign to take down Scientology once and for all. They posted a video called "Message to Scientology" and launched a crusade against the church, which included a coordinated attack on the organization's website.
And so a movement was born. Thousands of people showed up in real life to protests around the country. "It was a very bizarre scene," the former hacker Gregg Housh said of the protest he attended in Los Angeles. "Here is a church created by a science-fiction author, being protested by people wearing masks created by a science-fiction author." Reality was bending; the simulation was showing its cracks.
For the next decade, Anonymous would harness the Internet in unprecedented ways, fighting for justice and destruction, for irony and distraction, and for change that would reverberate all the way to the top.
WikiLeaks and the Arab Spring: Anonymous Gets Political
Anonymous quickly shifted focus towards censorship and free speech. They used DDoS (Distributed Denial of Services) attacks to shut down websites they viewed as threatening to freedom. In 2010, they emerged to protest a censorship bill in Australia; and later that year, they collaborated to defend WikiLeaks after Amazon kicked Julian Assange's operation off its servers and Visa, Mastercard, and PayPal stopped processing donations to the group. (Anonymous later separated itself from WikiLeaks, due to Assange's influence over the organization).
Around the same time, a segment of the group decided that they'd collectively become too serious. They needed more "lulz"—LOLs, laughs, the trolling ethos that originally inspired the group. So a group called Lulz Security (or LulzSec) was born. They hacked the CIA's website. The next month, the FBI arrested fourteen Anonymous hackers for the aforementioned earlier attacks on PayPal, and Anonymous began to rise on the US government's radar.
In 2011, when the Tunisian government blocked WikiLeaks, Anonymous launched a crusade to support protestors in the movement that would eventually spark the Arab Spring. One of the more infamous leaders of LulzSec, Hector Xavier Monseguer (or "Sabu")—who would later become an FBI informant—and others also allegedly helmed a DDoS attack on the Tunisian government's websites. Anonymous was also integral to the planning of 2011 Occupy Wall Street protests in New York, which were somewhat similar to the organization in that they lacked internal structure and clear leadership and set goals.
Soon, White House staff became concerned that the group could destabilize the US power grids. The group became known as cyber-terrorists and anarchists. Perhaps out of necessity, or because its major players were being taken out or growing up and leaving hacktivism behind, Anonymous fractured around 2015 and 2016, leaving behind conspiracies and a legacy of rupture and chaos.
Still, Anonymous's penchant for social action continued throughout the 2010s. In 2013, Operation Safe Winter fought to raise awareness about homelessness. In 2014, a group called "Operation Ferguson" organized cyberprotests against the police after the death of Michael Brown.
In 2015, Anonymous shifted its focus towards the Islamic State. #OpISIS was a response to the Charlie Hebdo attacks in Paris; despite being a largely uncoordinated effort, they still managed to make waves. "For more than a year, a ragtag collection of casual volunteers, seasoned coders, and professional trolls has waged an online war against the Islamic State and its virtual supporters," writes E. T. Brooking. But they never lost their irreverence.
"Taking away the free speech from a group that is advocating the end of free speech is delicious fun," a member wrote on a Reddit forum about the Hebdo operation.
"They rise up most forcefully when it comes to Internet freedoms and technology, particularly technology that is being abused in some way," says Brian Knappenberger, creator of the documentary We Are Legion. "They're sort of protectors of the Internet. This is their territory, and if it's abused, they're personally offended."
In the latter half of the 2010s, Anonymous waged war against pedophiles and the dark web. In 2018, they lashed out at QAnon, the pro-Trump conspiracy group that stole Anonymous's branding despite a complete lack of alignment with most of Anonymous's central ideologies.
Some members of Anonymous may have gone off to join QAnon; it's hard to know. Though different from Anonymous, QAnon shares some of Anonymous's hatred of the government—its "deep state" paranoia echoes Anonymous's fears of totalitarianism.
Today, QAnon members often show up at Trump campaign rallies, and though Anonymous and QAnon have very different ideas about what constitutes freedom and free speech, it's clear they both believe they're fighting for it.
In the wilderness of the Internet, especially when so many layers of irony interlace with each other and when trolls abound, it's easy for ideologies to twist out of form. It's easy for trolls to be mistaken as criminals, too—just as it's easy for trolls to become criminals. On the Internet, at least outside the realm of corporate influence and bribes, identity is as fluid and amorphous as you want it to be. Anonymous members can become Trump supporters who can become Bernie supporters who can become QAnon supporters who can become FBI informants who can then rejuvenate Anonymous.
If the Anonymous movement shows us anything, it's that identity and ideology are not set. They're as fluid as the shifting landscape of the World Wide Web, which might just be a reflection of the shifting tides of the human spirit.
Remembering Anonymous in 2020
If you Google Anonymous, you'll see the question "is anonymous good"? pop up on the search bar.
A short search will reveal that most self-proclaimed authorities on the subject believe that Anonymous is neither good nor evil. Instead, it's a diverse group made up of people from all around the world, bound together by a shared symbol rather than a structure or hierarchy.
Because Anonymous never had a set ideology or leader, there's no one precise way to remember them. There's no way to know what's real, or if Anonymous was ever the super-group that the media made it out to be. Most likely, it was more of an idea than anything else, though it may still exist in pockets. There's also no way to tell if the group has just gone further underground or if it truly has been dead for years.
According to Gabriella Coleman, Anonymous was always about freedom and elusiveness. "They dramatize the importance of anonymity and privacy in an era when both are rapidly eroding," she writes.
In terms of ethos, Coleman argues that Anonymous embodied an ancient trickster archetype, using old ideas about freedom, hedonism, and the randomness of the universe to cope with an increasingly unbearable modernity. "Nietzsche was attuned to the vitality of sensuality, myth, and art. Music, poetry, and even the mad laughter of the trickster Dionysus, who he championed, offer an aesthetic life of pleasure," she writes in her book Hacker, Hoaxer, Whistleblower, Spy: The Many Faces of Anonymous. "They are pursuits through which humans can overcome their limits and the tragic condition of life: 'Not by wrath does one kill but by laughter. Come, let us kill the spirit of gravity!'"
Is Anonymous nothing more or less than an idea, which became a movement and an identity? Was it all just a story? Has the story ended, or has it fractured and bled into other movements and other corners of the Internet?
Someone in a Guy Fawkes mask is out there, laughing.
The Anonymous forum on Reddit is still alive and well. A month ago, one Redditor mused, "Is Anonymous just a legend to teach us that we do not need a name or an organization to use our power?" Could Anonymous have been a myth designed to reveal that 'All of us can anonymously exploit the options that we have (elections, commercial decisions, jobs we chose, freetime activities) to change the world together?'"
Recently, #AnonHasBeenDeadForYears trended on Twitter. Some agreed with the hashtag. Some warned the world that Anonymous has never been dead—instead, it's everywhere.
These are the kind of conversations that Anonymous inspires. Half-ironic, half-imbued with radical visions—zombified, always mutating—Anonymous (or whatever remains of it) persists.
Maybe it persists in part because it, ironically, offered a form of identity, of differentiation, of meaning crafted through collectivity born out of a crisis of meaning. Perhaps in anonymity, there is identity.
"On the street...I am just another person in a sea of faces," writes a (fittingly) anonymous blogger in Dazed, in a piece that may or may not be a parody or a fake—we'll never know. "But in cyberspace we are different. We helped free the people of Egypt. We helped fight against Israel as it attempted genocide. We exposed more than 50,000 paedophiles around the world. We fought the drug cartels. We have taken to the streets to fight for the rights you are letting slip through your fingers. We are Anonymous."
Are you?
How Safe are Your Passwords?
Is it even worth changing your password?
As threats to personal cybersecurity become more and more acute, many websites have created mandatory password update policies, forcing users to switch their login info every few months. This is true of most universities and certain brands of operating systems–Microsoft is notorious for regularly prompting password changes. The theory as to how this helps keep you secure is simple. By regularly changing your passwords, you limit the amount of time other people who've stolen your password can access your account. Unfortunately, there does not seem to be much evidence that repeatedly changing your passwords works to make your accounts more secure.
According to a 2010 study conducted by Microsoft, mandatory password changes costs billions of dollars in productivity for the companies that enforce them. These changes usually force workers to comport to stringent requirements, such as using a specific number of capitalized letters and special characters. According to the study, all this does is make remembering one's password harder. Most people just make a slight variation to their already existing password, and In some cases they even put their new password on a sticky note near their computer, for anyone walking by to see. On top of this, password changes to high-risk accounts are largely ineffective. This is because when a hacker gets the login information to, say, your online bank account, they aren't going to sit around constantly logging on to spy on your finances. They're going to transfer your money as quickly as possible, and unless you change your password at the exact instant in which they're accessing your account, all the mandatory updates in the world won't help you. Essentially, mandatory password changing on most accounts is at best a meaningless headache and at worst a huge time waster.
There are certain types of accounts in which hackers may linger to gather certain information about you. If a hacker gets into your Facebook account, they may stick around for a few months, impersonating you or trying to use the things you've posted as a means of gaining access to your other accounts by determining the answers to your security questions. In this case, it may be worth changing your account regularly as a preventative measure. That said, the methods that today's hackers use are usually advanced enough to crack most passwords.
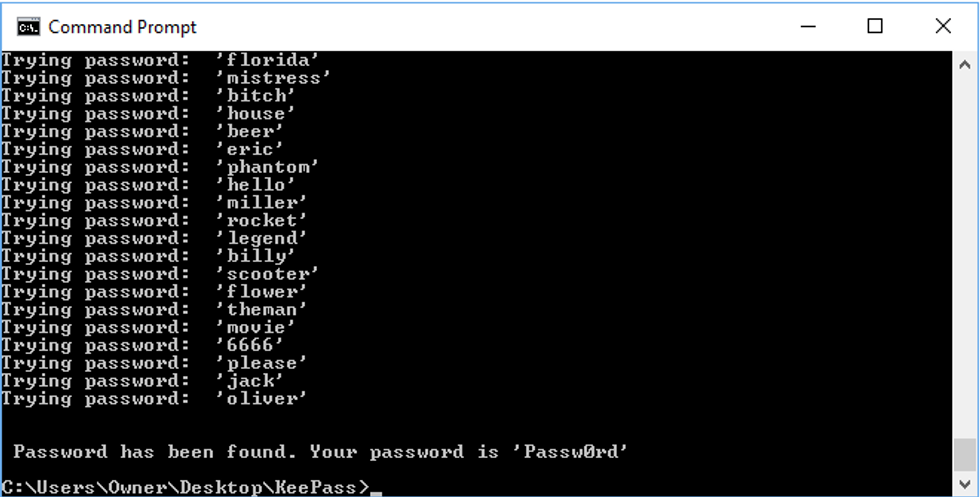
Dictionary attacks as their name implies, use a program that randomly combines and words from the dictionary, quickly guessing any password that doesn't contain proper nouns,numbers or special keys.
Brute force attacks take a serious amount of computing power but have the potential to guess any password if given enough time. They simply guess, very quickly, every possible password variation. The longer your password, the safer it is.
Rainbow table attacks are an advanced method of breaking a website's encryptions after stealing its password database. These databases are easily accessible but most are protected by cryptographic hash functions. These are functions that encrypt passwords, with minute changes in input drastically affecting the function's output. Rainbow tables often provide a more feasible means of attack than using brute force, as the passwords contained in them are already hashed, making comparisons much easier.
Even if the websites you use salt (attach random data to) their passwords and encryption hashes as a preventative measure, this may not be enough. When the passwords, usernames and personal information of Ashley Madison users were leaked, Ashley Madison–probably due to the nature of the site's information–was using an advanced function called bcrypt to salt all of their hashes. Unfortunately, they also used the antiquated but still very popular MD5 encryption function for certain portions of their database. Hackers didn't even need to attack the bcrypt in order to get the data they wanted. They just hit the MD5 tokens and were able to reveal most of the information on the site.

Unfortunately, these vulnerabilities are more or less systemic. There's no way to convince the owners of the websites you frequent to update their encryption functions or any concrete way for you to protect your passwords. In reality, your passwords are never truly safe, unless they're protected by bcrypt, which is really only safe until some cracks it. Your chances of being hacked, regardless of your password's sophistication, is virtually 100%. Hackers have programmed bots to do the heavy lifting and most attempts at hacking occur automatically. To make matters worse, there are large swaths of web that aren't even encrypted, and the areas that are, have been proven susceptible to attack. This means the answer to the question of how often you should change your passwords is relatively simple. You only need to change them if you think someone else has direct access to your account specifically. An angry ex or someone spying over your shoulder on the bus is a much more pressing danger than some anonymous hacker online. The truth is, changing your password won't do much to stop people who know what they're doing. Passwords only protect you because it takes effort to hack them, not because they're impenetrable.
What Is the Dark Web?
It's not as scary as you think.
There have been numerous pieces written about the dark web and the dangers it could pose to your personal cyber security. It's also been used in advertisements by Experian, in which they offer "free dark web scans" to help customers find out if their "information is on the dark web." This type of language is deliberately misleading, as is the company's definition of the dark web, which basically describes it as a world full of Internet marauders hunting for your social security number. Ironically, in order to acquire the "free dark web scan," Experian itself asks its customers for their social security numbers.
In a certain light, these ads are hilarious in their deliberate misinterpretation of how the dark web works, but there's something sinister about the way they prey on the wallets of the uninformed. Though it sounds dangerous, the dark web isn't the nightmarish hellscape that cyber security companies would have you believe it is. Before understanding the dark web however, one has to first understand the deep web, and by extension, the Internet as a whole.
The Internet is divided into two subsections: the surface web and the deep web. The difference between the two is simple. The surface web is readily accessible via search engines; the deep web is not. While almost every site you visit is probably part of the surface web, there are certain places on the Internet that are necessarily hidden. For example, research papers, netbanking, and medical records aren't readily accessible to anyone using Google, as the search engine doesn't index these things. Another example, is content that exists behind a paywall, like the New York Times' online newspaper. The dark web can be thought of as a small subsect of the deep web, but while the two are often conflated, they aren't the same at all. It's helpful to think of the Internet as an iceberg, with most of it existing beneath the surface. The surface web encompasses about 4% of the entire Internet while the deep web and dark web, represent 90% and 6% respectively.
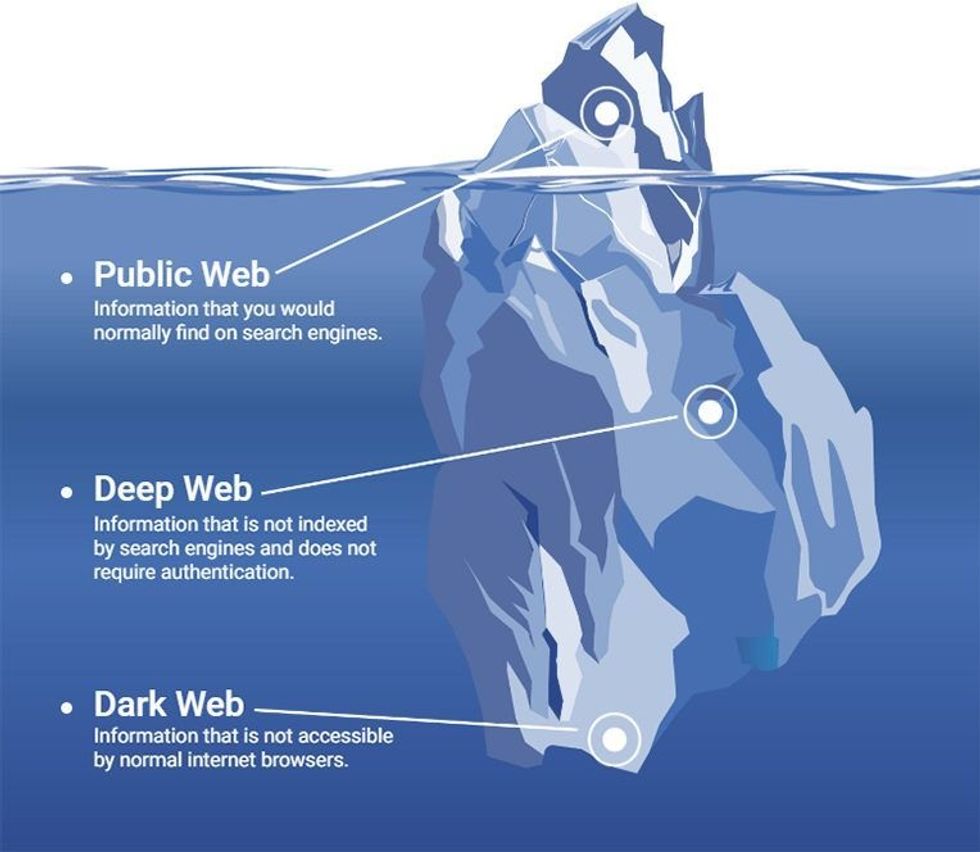
Unlike the deep web, the dark web is only accessible via special networks, the most popular of which being Tor. Browsers like Tor render your computer invisible while you browse, using complex encryptions to mask your computer's IP number while you browse, allowing for a truly private Internet experience. Confidentiality is at the heart of Tor's mission, and its developers goal was to create an Internet free of surveillance and tracking. Unfortunately, when they are guaranteed anonymity, many Internet users get into some pretty unsavory things.
The first time the dark web was in the news, was when the online black market the Silk Road became a major player in 2011. Until the FBI arrestedSilk Road founder Ross Ulbricht in 2013, the site was a forum dealing in illegal weapons, drugs, and child pornography, and the transactions were made via Bitcoin rather than actual cash. Bitcoin itself came to prominence in these illicit markets, though it's slowly falling out of favor with online black markets due to the wild fluctuations in its price over the past few years. Outside of the Silk Road and its successors, there has also been tons of publicity surrounding the hiring of hit men via the dark web, though most of these services have turned out to be scams. The most famous scam was run by a company called Besa Mafia, who would take cash from buyers, and then instead of killing the person they were hired to kill, they would report the buyers to the police and get them arrested.

Realistically though, the dark web isn't nearly as scary as it's made out to be. Yes, there are hackers and illegal activity, but at the core of Tor's project, is privacy. If a hacker wanted to steal someone's social security number or if a pedophile wanted to seek out illicit porn, they wouldn't need to use the dark web to do it. In fact, the dark web only accounts for about .2% of the child porn being shared online. While it's fair to assume that most sites on the dark web are used for criminal activity, it's worth mentioning that the FBI can pretty easily arrest and track folks using the dark web. They've even contracted one of Tor's developers to help them track down cyber criminals.
The dark web's reach with regard to criminal activities has been largely exaggerated by the mainstream media, and there's no real reason to fear it. If you're someone who strongly values the privacy of your browsing habits, for whatever reason, the dark web provides a different type of Internet, one that's far more secure than your standard browser. If you don't care about your Internet privacy, that's fine too. Dark web hackers aren't going to hunt you down and steal all your information in the night, and you're no less safe on the Internet just because Tor browsers exist. There's a strange tendency in this country to conflate others' privacy and anonymity with a lack of personal security. Cyber security firms have a vested interest in keeping you scared and in the dark about how the Internet works. Don't put too much stock into it. The dark web as we know it has existed since 2002, and we're no worse for wear.


