As threats to personal cybersecurity become more and more acute, many websites have created mandatory password update policies, forcing users to switch their login info every few months. This is true of most universities and certain brands of operating systems–Microsoft is notorious for regularly prompting password changes. The theory as to how this helps keep you secure is simple. By regularly changing your passwords, you limit the amount of time other people who’ve stolen your password can access your account. Unfortunately, there does not seem to be much evidence that repeatedly changing your passwords works to make your accounts more secure.
According to a 2010 study conducted by Microsoft, mandatory password changes costs billions of dollars in productivity for the companies that enforce them. These changes usually force workers to comport to stringent requirements, such as using a specific number of capitalized letters and special characters. According to the study, all this does is make remembering one’s password harder. Most people just make a slight variation to their already existing password, and In some cases they even put their new password on a sticky note near their computer, for anyone walking by to see. On top of this, password changes to high-risk accounts are largely ineffective. This is because when a hacker gets the login information to, say, your online bank account, they aren’t going to sit around constantly logging on to spy on your finances. They’re going to transfer your money as quickly as possible, and unless you change your password at the exact instant in which they’re accessing your account, all the mandatory updates in the world won’t help you. Essentially, mandatory password changing on most accounts is at best a meaningless headache and at worst a huge time waster.
There are certain types of accounts in which hackers may linger to gather certain information about you. If a hacker gets into your Facebook account, they may stick around for a few months, impersonating you or trying to use the things you’ve posted as a means of gaining access to your other accounts by determining the answers to your security questions. In this case, it may be worth changing your account regularly as a preventative measure. That said, the methods that today’s hackers use are usually advanced enough to crack most passwords.
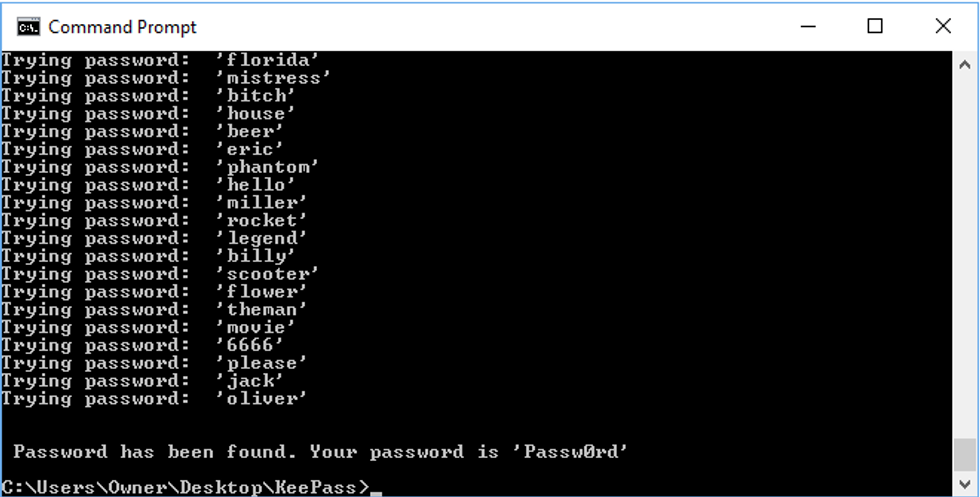 Dictionary attack
Dictionary attack
Dictionary attacks as their name implies, use a program that randomly combines and words from the dictionary, quickly guessing any password that doesn’t contain proper nouns,numbers or special keys.
Brute force attacks take a serious amount of computing power but have the potential to guess any password if given enough time. They simply guess, very quickly, every possible password variation. The longer your password, the safer it is.
Rainbow table attacks are an advanced method of breaking a website’s encryptions after stealing its password database. These databases are easily accessible but most are protected by cryptographic hash functions. These are functions that encrypt passwords, with minute changes in input drastically affecting the function’s output. Rainbow tables often provide a more feasible means of attack than using brute force, as the passwords contained in them are already hashed, making comparisons much easier.
Even if the websites you use salt (attach random data to) their passwords and encryption hashes as a preventative measure, this may not be enough. When the passwords, usernames and personal information of Ashley Madison users were leaked, Ashley Madison–probably due to the nature of the site’s information–was using an advanced function called bcrypt to salt all of their hashes. Unfortunately, they also used the antiquated but still very popular MD5 encryption function for certain portions of their database. Hackers didn’t even need to attack the bcrypt in order to get the data they wanted. They just hit the MD5 tokens and were able to reveal most of the information on the site.
 This idea of a hacker is a bit cartoonish
This idea of a hacker is a bit cartoonish
Unfortunately, these vulnerabilities are more or less systemic. There’s no way to convince the owners of the websites you frequent to update their encryption functions or any concrete way for you to protect your passwords. In reality, your passwords are never truly safe, unless they’re protected by bcrypt, which is really only safe until some cracks it. Your chances of being hacked, regardless of your password’s sophistication, is virtually 100%. Hackers have programmed bots to do the heavy lifting and most attempts at hacking occur automatically. To make matters worse, there are large swaths of web that aren’t even encrypted, and the areas that are, have been proven susceptible to attack. This means the answer to the question of how often you should change your passwords is relatively simple. You only need to change them if you think someone else has direct access to your account specifically. An angry ex or someone spying over your shoulder on the bus is a much more pressing danger than some anonymous hacker online. The truth is, changing your password won’t do much to stop people who know what they’re doing. Passwords only protect you because it takes effort to hack them, not because they’re impenetrable.
- We Are Anonymous: A History of the Elusive Hacktivist Collective – Liberty Project ›
- How To Set Up Your Tech So You Won’t Be Hacked – Liberty Project ›